Introduction
There has been a lot of talk in various forums about how to get Outlook Anywhere to work with NTLM authentication through ISA Server 2006. This has also been a high priority for me since single-sign on is a great feature. Users, when logging on from domain joined computers, should not have to enter their network credentials when accessing any service on the corporate network. This post will explain one way of setting up Outlook Anywhere to use single-sign on. I use Outlook 2007 and Exchange 2007 in my set up. Perhaps this is also possible with Exchange 2003 and Outlook 2003, but I have not investigated that. I also make certain assumptions about the readers of this post; I assume you are well versed in both ISA 2006, Exchange 2007 and Window Server terminology and functionality, this is not a detailed step-by-step guide.
The set up
I have 4 machines participating in this set up:
- LAB-DC1: A Windows Server 2003 R2 Domain Controller
- LAB-ISA: A Windows Server 2003 Server running ISA Server 2006 (with the Exchange 2007 publishing patch)
- LAB-EXCH: A Windows Server 2008 (x86) running Exchange 2007 Service Pack 1 (Mailbox, Hub Transport and Client Access Server)
- VISTA01: A Windows Vista with Service Pack 1 client running Outlook 2007 with Service Pack 1.
The three servers are all on the internal network, while the Windows Vista client is on the Internet. The ISA server is publishing Outlook Anywhere.
Fixing the Windows Server 2008/Exchange 2007 SP1 IPv6 bug
The DS proxy component of Exchange 2007 has a bug where it does not listen on the IPv6 addresses of a server. This causes Outlook Anywhere clients not to be able to connect to Domain Controllers and query Active Directory. The clients can successfully connect to the Exchange server using MAPI, but Active Directory access does not work. The way to fix this depends on what Exchange set up you have. If you have the CAS role on a separate server you need to follow these steps (from the MSExchange Team blog):
- Unselect IPv6 from the properties of your NIC (on the RPC-over-HTTP Proxy machine); that will force the RPC-over-HTTP Proxy to use IPv4 to talk to Exchange and everything will be fine. In most cases, this step suffices. If it does not, continue with steps 2 and 3.
- Under the regkey HKLM\SYSTEM\CurrentControlSet\Services\Tcpip6\Parameters, add a 32 bit DWORD with the name Disabled Components and value 0xFF
- Reboot the machine
If you’re in a single-server scenario where the RPCProxy and Mailbox are on the same machine, then the above does not work since the loopback interface still uses IPv6. In this case, you need to make the following changes in the system32\drivers\etc\hosts file:
- Comment out the line “:::1 localhost”
- Add the following two lines:
<IPv4 address> <hostname of the computer>
<IPv4 address> <FQDN of the computer>
A more thorough explanation of this issue can be found here, as well as a good description of how Outlook Anywhere works:
http://msexchangeteam.com/archive/2008/06/20/449053.aspx
http://blog.aaronmarks.com/?p=65
How to set up Outlook Anywhere with Single-Sign On
Exchange 2007
- If you have not already done so; install the RPC Proxy component on the CAS server.
- Enable Outlook Anywhere on the CAS server:
Enable-OutlookAnywhere –DefaultAuthenticationMethod Ntlm –ExternalHostName outlook.lab.com - Install an SSL certificate on the web site hosting Outlook Anywhere.
This certificate must contain the public name where you are hosting Outlook Anywhere, as well as any other names that is required in your setup. - Configure the OAB to use HTTPS:
Set-OabVirtualDirectory –Identity ‘LAB-EXCH\OAB (Default Web Site)’ –RequireSSL $true - Set the external name of the OAB virtual folder:
Set-OabVirtualDirectory –Identity ‘LAB-EXCH\OAB (Default Web Site)’ -ExternalUrl https://outlook.lab.com/OAB -InternalUrl https://lab-exch.lab.net/OAB - Export the SSL certificate and install it on the ISA server.
ISA Server 2006
Create a standard publishing rule for Exchange2007 Outlook Anywhere; select to publish additional folders for Outlook 2007 clients:

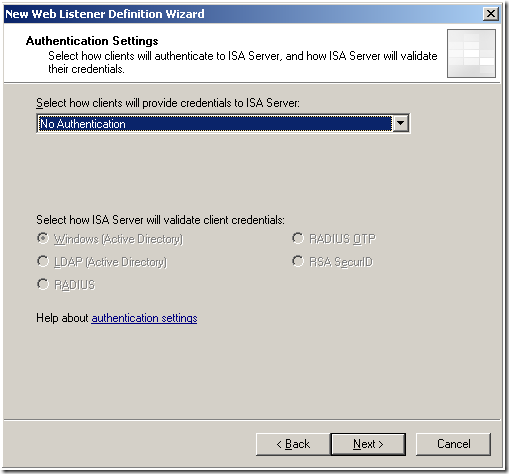
- During the creation of the publishing rule; create a new listener for Outlook Anywhere, on the Authentication page, select No Authentication:
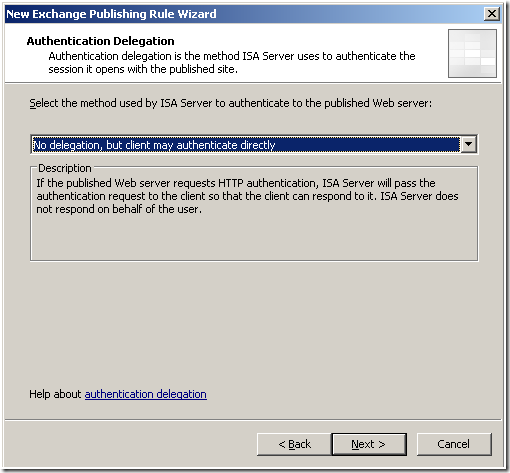
- Back in the rule wizard, select the No delegation, but client may authenticate directly option:
Client/Outlook 2007
- Start Outlook 2007 on the client, while it is connected to the internal network. This will cause Outlook to contact the Autodiscover service and automatically configure itself for regular MAPI/RPC operations as well as Outlook Anywhere (HTTP):
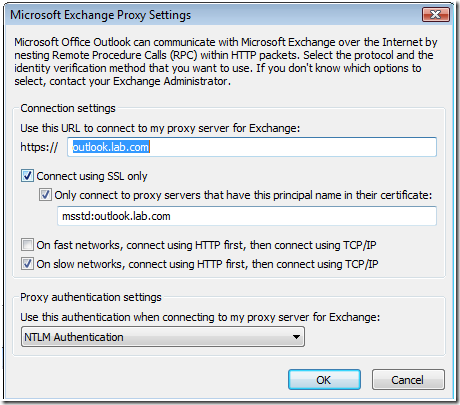
- Disconnect the client from the internal network and connect it to the Internet. Open Outlook:

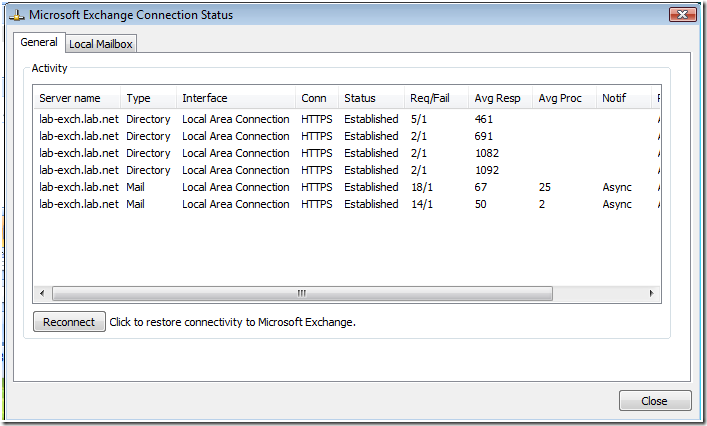
Outlook will connect to Exchange without requiring a username or password. The Connection Status box will show a successful connection:
- Run the Test E-mail AutoConfiguration tool:
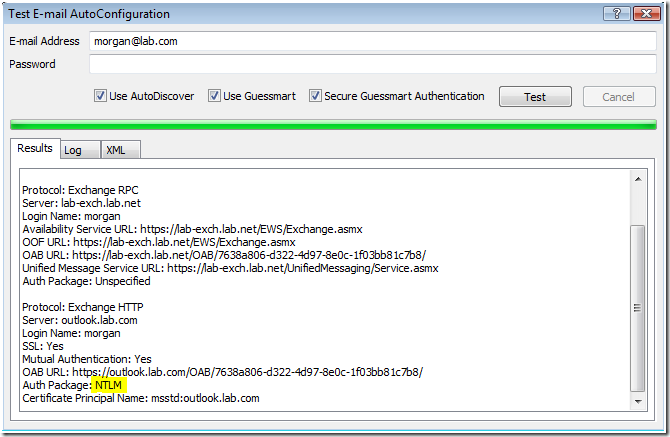
As you can see the Autodiscover service was successfully contacted. The AS service is also set to accept NTLM by default.
How it works/notes on security
This setup allows the client to directly authenticate to the Exchange 2007 CAS server, reducing the ISA Server computer to a mere reverse proxy, only performing HTTP inspection, you lose the benefit of ISA pre-authentication. This should not be a major problem, but should be evaluated carefully before implementing in your network.
Unexpected password prompts
If the Outlook client is left untouched for extended periods of time, typically over 1 hour, the connection to the Exchange server is somehow severed, and Outlook will prompt the user for their username and password. You will not be able to reconnect even if you enter the correct username and password. I think this is because ISA server terminates the connection between the Exchange server and Outlook if it is left unused for a long time. The way to recover from this situation is by either restarting the IIS services on the Exchange server or the Firewall service on ISA server. Further investigation is needed to determine the exact cause of this problem.
Conclusion
This has been a quick guide to achieving single-sign on for Outlook Anywhere with Exchange 2007 and Outlook 2007. With this setup you lose ISA pre-authentication. There may be another way to achieve the same result using Kerberos Constrained Delegation (KCD), that will be the topic of a future post.
